Makaleler
21
Tümü (21)
SCI-E, SSCI, AHCI (17)
SCI-E, SSCI, AHCI, ESCI (19)
ESCI (3)
Scopus (19)
Diğer Yayınlar (2)
3. Faster NTRU on ARM Cortex-M4 With TMVP-Based Multiplication
IEEE TRANSACTIONS ON CIRCUITS AND SYSTEMS I-REGULAR PAPERS
, cilt.69, sa.10, ss.4083-4092, 2022 (SCI-Expanded, Scopus)




6. Cortex-M4 optimizations for {R, M} LWE schemes
IACR Transactions on Cryptographic Hardware and Embedded Systems
, cilt.2020, sa.3, ss.336-357, 2020 (Hakemli Dergi)
8. Faster Residue Multiplication Modulo 521-bit Mersenne Prime and an Application to ECC
IEEE TRANSACTIONS ON CIRCUITS AND SYSTEMS I-REGULAR PAPERS
, cilt.65, sa.8, ss.2477-2490, 2018 (SCI-Expanded, Scopus)




9. New Efficient Algorithms for Multiplication Over Fields of Characteristic Three
JOURNAL OF SIGNAL PROCESSING SYSTEMS FOR SIGNAL IMAGE AND VIDEO TECHNOLOGY
, cilt.90, sa.3, ss.285-294, 2018 (SCI-Expanded, Scopus)




10. Efficient Big Integer Multiplication in Cryptography
journal of information security
, 2017 (Hakemli Dergi)
18. Efficient multiplications in F(5)5n and F(7)7n
JOURNAL OF COMPUTATIONAL AND APPLIED MATHEMATICS
, cilt.236, sa.2, ss.177-183, 2011 (SCI-Expanded, Scopus)




Hakemli Bilimsel Toplantılarda Yayımlanmış Bildiriler
21
6. Efficient GeMSS Based Ring Signature Scheme
The Second International Workshop on Cryptography and its Applications – 2’IWCA’19, Oran, Cezayir, 18 - 19 Haziran 2019, (Tam Metin Bildiri)
9. GUI Based Ring Signature Scheme
18th Central European Conference on Cryptology (CECC 2018), Smolenice, Slovakya, 6 - 08 Haziran 2018, ss.1-3, (Tam Metin Bildiri)
11. How Cryptology Affects Digital Life and Transformation
Digital Transformation, 28 Aralık 2017, (Özet Bildiri)
12. Efficient Big Integer Multiplication in Cryptography
ISCTurkey, 25 - 26 Ekim 2017, (Tam Metin Bildiri)


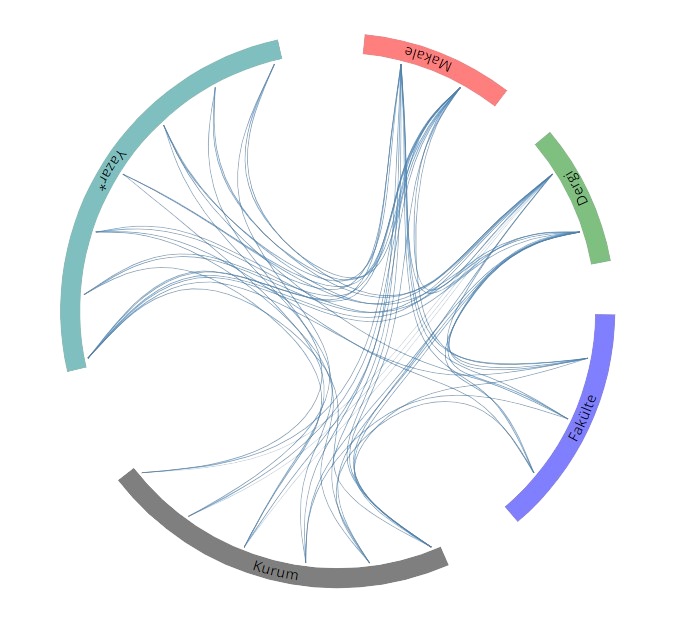 Yayın Ağı
Yayın Ağı
